Notifications
Receive real-time notification e-mails when a new counterfeit version of your applications is detected.
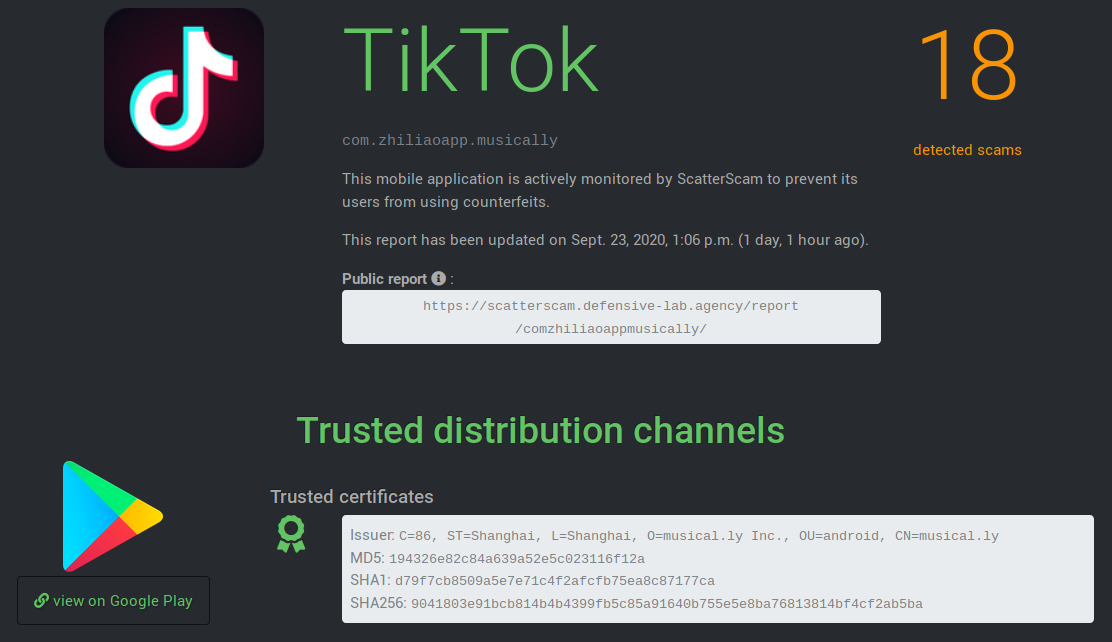
ScatterScam:
detect and identify counterfeit Android applications
The big picture
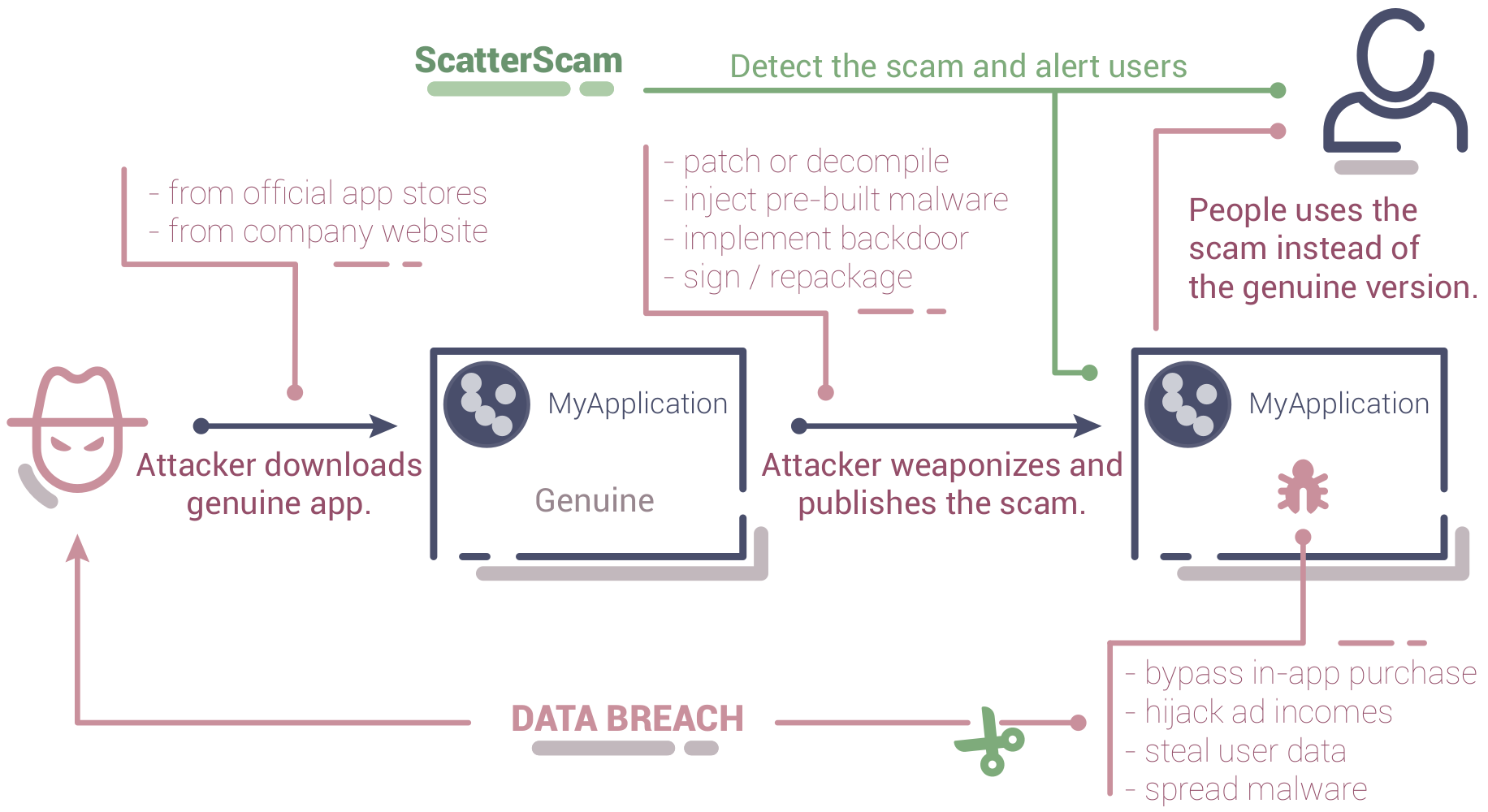
What a counterfeit application is?
It is an application that, most of the time, acts exactly like the official application: it offers the same services, the same functionalities; it is visually identical; but it has been modified to incorporate malicious code.
This malicious code can, for example: cause data leaks (including sensitive data such as login credentials), abuse the permissions granted to your application for illegitimate use.
The main levers sought by attackers to choose your application as an attack vector are most of the time: your brand image, your notoriety, the trust your customers offer you.
Features
AV detection
Receive up-to-date anti-virus alerts when counterfeit versions of your application is detected.
Attribution
Know where counterfeit versions of your application are distributed and who is behind the scam campaign.
Risk assessment
Get insights into the behavior of the counterfeit versions to know the risks your business and users face.